Dirk Schrader, resident CISO (EMEA) and VP of security research at Netwrix
netwrix.com
The UK is in a state of cybersecurity transition. Following Britain’s exit from the European Union (EU), the country is now disengaging from the previous GDPR data security legislation of the EU. In its place comes the UK Data Reform Bill, which aims to create “new data laws to boost British business [and] protect consumers.” Within this legislative framework, as “the same high data protection standards will remain”, UK organisations must make use of best data security practices or else risk reputational fallout and possibly hefty fines.
This transition comes at a precarious time in the state of global cybersecurity. Advanced persistent threats (APTs) are ever-evolving, and cybercriminal groups are becoming increasingly sophisticated in their methods to pilfer organisational data. In the face of these challenges, UK organisations must employ leading strategies to keep both themselves and their customers safe. Here, zero-standing privilege can play a vital role as it drastically reduces the attack surface available for cybercriminals and increases the detectability of their actions.
What is zero-standing privilege?
As workforces continue with remote and hybrid work models, this can make organisations especially vulnerable to escalating cybercrime and open gaps in business-wide security standards. Adopting the zero-standing privilege approach helps to significantly decrease the attack surface and mitigates the risk of infiltration.
So, what exactly is zero-standing privilege and what does its implementation entail for organisations?
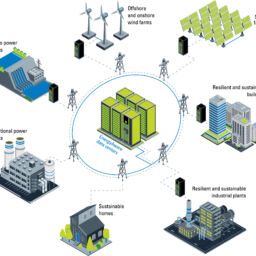
Basically, zero trust is a strategy for securing an organisation’s IT assets, including data, identities and infrastructure with data being first among equals since it is the attackers’ ultimate goal. With zero-standing privilege, access to resources from both inside and outside of the network can be restricted until the validity of the request is confirmed. Every user, regardless of who they are in the organisation, must still go through specific procedures to verify their identity to be authorised for the secure level of access they seek.
Zero-standing privilege as a policy ensures that users and services verify their credentials when gaining access to organisational resources, so it’s far harder for unauthorised users to move adjacently through targeted infrastructure right to the company sensitive data. This can be maintained by an automated process through which requesting access to databases is vetted to make sure the accessing user is not hostile on a continual basis. This approach is especially important when it comes to privileged accounts which give access to more critical resources compared to the accounts of regular users. As the right to use a resource is removed once the session is closed, there is no residual risk from standing privileges.
Many organisations use a hybrid model that combines zero-trust principles with perimeter-based protection while they work to reinforce and modernise their IT infrastructure and business processes. This subsequently leads to companies carrying zero-trust policies alongside more traditional security workflows.
The benefits of zero-standing privilege for fast yet secure cloud adoption
For organisations looking to maintain holistic cybersecurity and facing business pressure for rapid digitalisation, the zero-standing privilege approach can bring myriad benefits. With 54% of workloads expected to be in the cloud in 2023 compared to 41% as of March 2022, it is crucial to address transitional cybersecurity risks. According to Forrester, more than three-quarters of the surveyed decision-makers cited the importance of a zero trust strategy to combat mounting security threats associated with cloud transformation and migration.
The cloud represents both an important resource and vulnerability for UK companies with research showing that 88% of organisations store sensitive data in the cloud. Of this data, 65% was personally identifiable information (PII) of customers, 42% was the PII of company employees and 31% was corporate financial information. Threats to this data were ubiquitous with 52% of surveyed companies reporting a cyberattack on their cloud infrastructure within the last 12 months. Of these attacks, phishing was the most widespread at 69% of reported incidents, followed by account compromise at 35% and targeted attacks against cloud infrastructure at 31%.
Given the oftentimes complex and interconnected nature of cloud use across enterprises, organisations might choose to use a hybrid model by implementing zero-standing privilege approach alongside more traditional security workflows.
The future lies in zero-standing privilege
As company digital infrastructures become increasingly complicated with a greater reliance on various cloud models, and cybersecurity threats become more ubiquitous and evolved, zero-standing privilege will serve an important role for organisations looking to keep their data safe. A process of continuous verification is vital in stopping threat actors once they have gained access to the network and limiting the damage they can wreak. This approach will keep UK companies in compliance with the UK’s replacement to GDPR and will help organisations avoid damage to their reputation and significant fines that often result from a breach.