By Sanjay Radia, Chief Solutions Architect at NETSCOUT
Traditionally, the best solution for defending businesses against potential compromises was by establishing a strong external perimeter – an outer boundary between an organisation’s own network and the outside networks which neighbour it. Nowadays, however, this concept is no longer applicable. Perimeter-based networks no longer have the necessary access controls to be able to detect or prevent cyberattacks, due to the ever-growing threat surface and evolution of attack vectors. An example of this can be seen with direct attacks such as the log4j vulnerability – a major susceptibility in the widely-used logging tool Log4j – in addition to indirect attacks, which includes phishing or malware attack.
Furthermore, when we consider the implicit security assumption that organisations can trust everything inside their own networks, things can only get worse. This assumption provides cyber criminals with the ability to navigate laterally within networks, as long as they’re inside it, enabling them to discover an additional compromise. Instead, introducing a zero-trust architecture is designed to improve the network’s overall cybersecurity strength, while permitting services which drive digital transformation.
What is zero trust?
As stated by the UK’s National Cyber Security Centre (NCSC), “Zero trust is an architectural approach where inherent trust in the network is removed, the network is assumed hostile and each request is verified based on an access policy.” Several different factors are required for a request to be regarded as trustworthy, including authorisation, access to valuable data, strong authentication, and the well-being of the device.
The zero trust design principles which have been incorporated by the NCSC provide a new approach when it comes to resolving a longstanding issue faced by businesses – securing information and networks. As such, companies across a wide range of industries are reconsidering their approach toward security, incorporating zero-trust features into their security architecture, processes and procedures.
One example of a zero-trust principle is multifactor authentication (MFA). Requiring additional factors to prove users’ identity prior to being able to access a resource – for example, scanning their fingerprint or confirming a pin sent to their mobile device – MFA adds an extra layer of security for networks and systems. Looking at this from a zero-trust point of view, MFA is used to verify an organisation’s own security measures, ensuring that those with access to the network are who they are claiming to be. This level of security markedly reduces the opportunity for cybercriminals to use compromised credentials to access a business’s data, devices, networks and systems.
Building a safe and secure domain
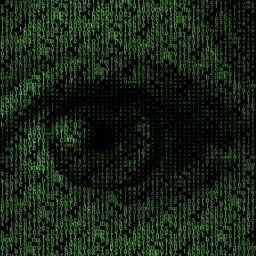
The zero-trust model can be envisioned as a group of pillars which represent different aspects of security, from devices and applications to users and networks. However, underneath these pillars are the foundational elements of a zero-trust architecture: analytics, automation, governance and visibility.
When it comes to adopting a zero-trust security model, the process tends to be continual and steady. At the start, enterprises tend to finetune their architectures, ensuring their solutions are near to becoming fully integrated across the aforementioned pillars. This allows businesses to become increasingly dynamic in terms of their decision-making regarding policy implementation.
While installing and building a zero-trust model may take time, the architecture will constantly be improved through the upgrading of policies, processes and tools. Nonetheless, the verification and ongoing auditing of zero-trust architectures remains imperative to understanding and exhibiting that a company’s security measures are both strong and effective.
One key feature of a zero-trust model is that it comes with no false sense of security – it is effectively ‘perimeter-less’ security. This differs greatly from conventional perimeter-based architectures, where anything happening inside of the network was perceived as being trustworthy, based on the assumption that in order to be in the network, users must have successfully progressed through the authentication stage and are permitted to be there. As such, this model believes that insiders provide no potential threats to the organisation and that perimeter security is unblemished. In contrast to this, zero-trust architecture puts an emphasis on providing protection against possible insider threats, thus preventing threat actors from gaining access to the system through the use of compromised credentials.
At the point at which an enterprise decides to implement a zero-trust model, it must ensure it has comprehensive visibility of the entire network. As well as this, the architecture must contain network taps which are capable of mirroring traffic from the wire, in addition to a tool which has the capacity to replicate and distribute packets to pre-existing cybersecurity monitoring applications. By ensuring the architecture includes these features, organisations can rest assured that their zero-trust model is effective.
This level of full-scale visibility will enable organisations to identify possible threats, track interconnected devices, observe historical usage, and offer their support in orchestrating mitigation through application programming interfaces (APIs). Furthermore, businesses should be capable of utilising protection groups in order to classify networks, servers and services, determined by the potential amount of damage which could be inflicted on them. This will put organisations in a strong position to swiftly adopt a zero-trust model.
Irrespective of where an organisation is in its zero-trust implementation journey – be it at the beginning or already well on its way – it is imperative to make certain that analytics and visibility are major features inside the detection and validation of the design which underpins the zero-trust architecture.