https://www.integrity360.com/
Brian Martin, Head of Product, Strategy and Innovation at Integrity360
How do you know how much to spend on cyber security and, how and where do you allocate the spend? These are questions every organisation should have at the top of its agenda. Cyber economics and spending should evolve faster than the cyber threats it’s being allocated to.
While convincing C-level executives to fund a better cybersecurity strategy is still a battle, the bigger challenges are now focused on the key security spending categories, how to optimise security spending and considerations for insourcing vs outsourcing.
As cyberattacks ramp up around the world, businesses and other organisations will continue to shell out more money on security tools and technologies. Benchmarking is one of the ways of determining whether you’re spending enough money in the right areas. Organisations should take a category-based approach and assign budgets to the necessary areas based on company needs and consider what peers are spending on their cyber security strategies.
Another good indicator of how much your business should be spending on security can also come from how much it allocates per employee. This provides a baseline to derive the figure that the average organisation spends as a whole to protect against common cyber threats.
The focus of this year’s Cyber Security Awareness month was on the dangers posed by phishing and ransomware attacks and these are areas where cyber spending is critical.
Phishing remains the most popular form of cyberattack, simply because it is easy, and it works. With phishing and ransomware incidents showing no signs of decline, cyber security awareness and training are vital for businesses and organisations of all sizes.
An organisation’s workforce is the front line of defence in keeping many types of cyberattacks at bay. Companies are now understanding that investing in employee awareness training is essential in reducing the number of entry points that threat actors have when infiltrating an enterprise network. Threats should be addressed on an ongoing basis and budget spend adapted to suit. It should not be considered a tick box exercise. Employee security awareness is an ideal place to start when discussing budget spend at any time of year, however, it is, in itself, not sufficient to fully address the human side of cyber security. Training and awareness should be but one component in a wider set of initiatives to build lasting security culture and embed the right behaviours within your organisation.
Backup or be sorry – Jon Fielding, Managing Director of EMEA, Apricorn
Ransomware and phishing are the key themes for this year’s Cybersecurity Awareness month – no crystal ball gazing at what threats lie ahead, but simply looking at those that continue to make waves and have devastating effects on businesses and consumers on a daily basis. A recent Apricorn survey found that, when IT decision makers were questioned on the main causes of data breaches within their organisation, phishing emails continued to rank at number one, with 40% citing it as the main cause of a breach.
Cyberattacks and ransomware schemes have affected organisations of many sizes across all industries and having an effective approach to cybersecurity begins with key fundamentals like using strong passwords and a password manager, enabling multi-factor authentication, updating software, and knowing how to recognise and report phishing.
In order to strengthen their security posture, organisations must tackle the issue of cyber risk at its root. This means underpinning the introduction and integration of any new technologies and tools by reverting to back to basics – understanding and improving the security posture, educating users, and implementing end-to-end encryption – so that organisations can remain secure as their operating environment continues to shift.
Additionally, individuals and organisations who want to be cyber Smart need to implement data backup policies like the ‘3-2-1 rule’: have three copies of data, on two different media, one of which is offsite for improved data resiliency.
Privileged and protected – Mark Warren, Product Specialist, Osirium
It’s easy for businesses and individuals to become complacent with varying aspects of cyber security, particularly those working remotely. Following the pandemic, many businesses had to adapt security processes to address quick fixes and temporary measures put in place and prepare for a more permanent adoption of remote and flexible working. However, it’s clear that many still have to consider the security of endpoint devices, especially those with shared usage.
Embracing Cyber Security Awareness Month, and the drive to encourage businesses to take a risk-based approach and focus on the behaviours most important to organisations, it’s clear that getting the basics in place is critical but, endpoint management is something all organisations should have in place.
With the move to remote working during Covid, staff members were often granted local admin rights on their laptops so they could get working without help from IT. Unfortunately, that means IT lost visibility and control over those laptops and remote workers could easily be duped into installing infected software, even if they’ve had the best cyber security awareness training. In addition to ensuring employees use strong passwords and MFA, privileged endpoint management (PEM) should be used to allow staff to run approved applications with elevated privileges. They can do their work without having wide-open access that attackers are looking for to install their malware.
With tools such as PEM deployed and active, businesses can balance productivity and security. Users can do the work they need with few calls to the Help Desk. IT gets fewer interruptions and can focus on more valuable work, auditors can see who had access to which applications, and logs show the actual users, not an arbitrary administrator account, ensuring security and compliance regs are met.
Proactive Security: Threat Intelligence – Scott Goodwin, Co-Founder and COO, DigitalXRAID
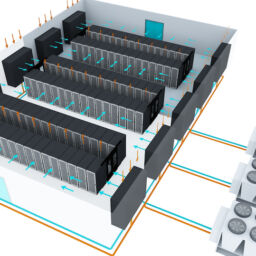
One area that has come up time and time again is proactive security and Security Operations Centre (SOC) services like threat intelligence. The importance of threat intelligence is underscored by the need for organisations to understand and gain visibility over the most severe threats facing their networks at any given time. Drawing on actionable insights from threat research and analysis, security teams are able to proactively defend against and detect attackers, limiting both the likelihood and severity of a breach.
However, many companies lack the resources and expertise to automate this data correlation and analysis process, which can be a huge drain on internal resources. This is why outsourcing a SOC is becoming increasingly popular and enterprises with limited budgets and expertise in-house are turning to external SOC providers to monitor events inside and outside of a network 24/7/365.
Buy-In from the Board – Rick Jones, Co-Founder and CEO, DigitalXRAID
IT teams often struggle to secure additional cybersecurity budgets – owing to a siloed department structure between themselves and senior management who make budgetary decisions – and find it challenging to quantify return on investment for security.
As the threat landscape becomes ever-more dangerous, with phishing and ransomware threats continuing to rise, it is vital that technical security teams and senior management work together and communicate in one common language: risk. Using a risk-based approach when seeking buy-in from the board helps to highlight a business’ exposure and, importantly, quantifies the financial impact if this risk were to be exploited.
Ultimately, risk can never be removed entirely; there will always be new threats and vulnerabilities that can cause damage to a business. The aim is therefore to measure risk and reduce it to an acceptable level. And this can only be achieved by communicating to the board in a shared language they understand.